At Trustack, we don’t do basic.
Our Beyond IT Support packages ensures that your business will have the best possible
protection – a carefully curated tech stack that we place our trust in.
Today, digital ways of working are relied upon absolutely. Productivity, flexibility, and remote collaboration have allowed people to work much more effectively.
The issue is, the attack surface for cyber criminals is expanding. Security software that did the job two years ago won’t cut it against the threats of today, nor does it suit the way we work.
Our team is dedicated to seeking out and delivering the most effective, innovative cybersecurity solutions on the market. We never offer anything we don’t use ourselves.
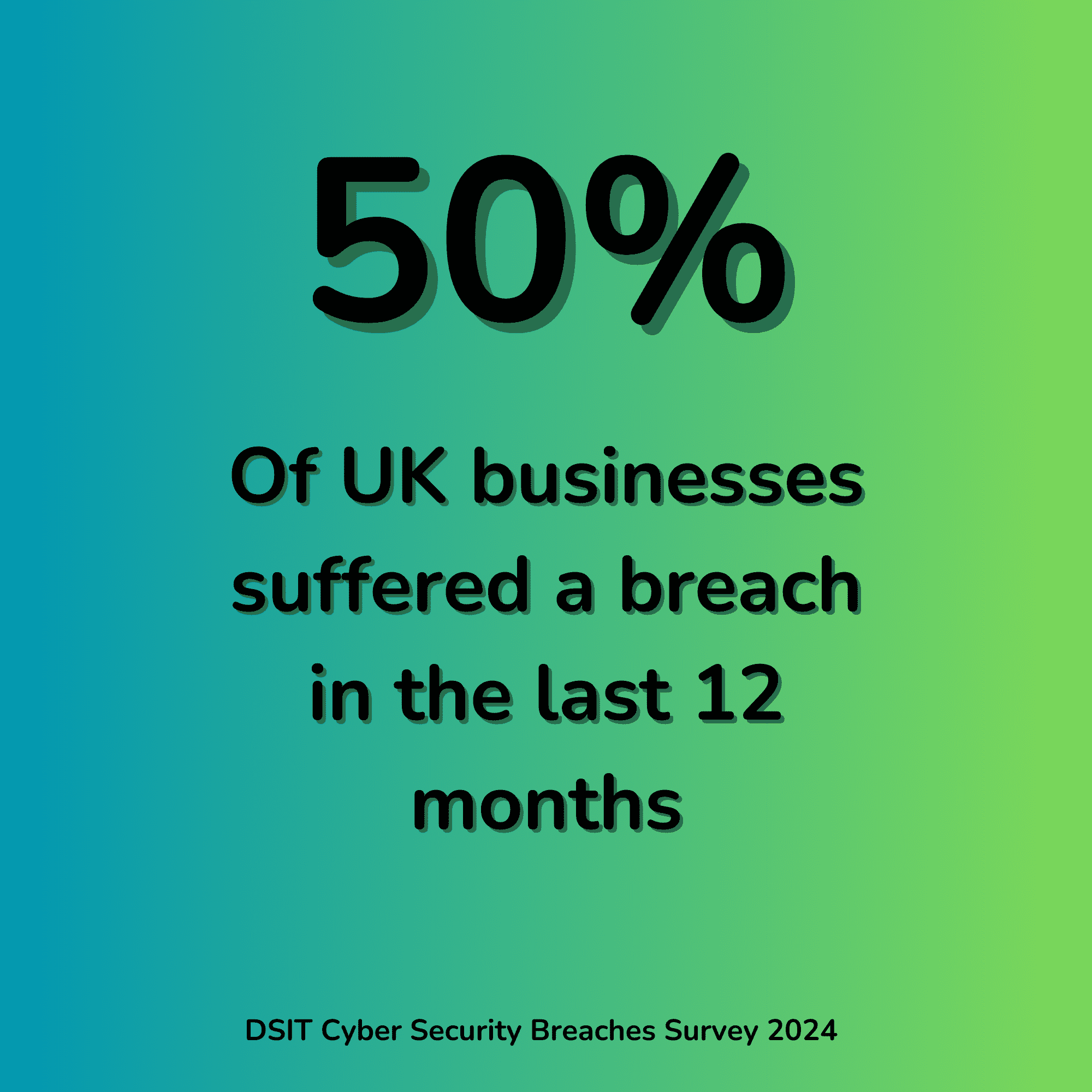
Keeping on top of cyber threats takes more time and resources than most companies have. Even with the right tools in place, breaches are a matter of when, not if; early awareness will allow you to recover fast in the event of a breach.
Since 2008, we have been protecting businesses like yours, and our customers stay with us. With customer satisfaction well above 90% (check our site for the live score!), we have partnership that go back as long as we’ve been doing business.
Our support packages have been designed to cover the security needs of business ranging from small, owner-managed operations to enterprise clients with thousands of employees.
Depending on your in-house capacity, we can go so far as to manage security on your individual endpoints, network, and data storage – or simply support your IT team with a patch management regime or remote monitoring of your Windows servers.
Every aspect of our Beyond packages have the latest security software protecting it, and we have an entire team dedicated to making sure your stack is up to date as well.
Ask us how quickly you could get support in place:
To provide the best experience on our site, we use technologies like cookies to store and/or access device information. Consenting to these technologies will allow us to process data such as browsing behaviour or unique IDs on this site.